Summary: As organizations are moving their workloads, data, and applications to the cloud infrastructure, incorporating security protocols is important to avoid any data theft. Let’s analyze the role of cloud security tools in implementing and managing security policies.
Transferring all the workload and data to the cloud infrastructure has helped businesses stay competitive and scale up their resources efficiently. However, it also makes their data and resources prone to security breaches. That’s where using a cloud security tool has become essential to keep all the data secure from cyberattacks, misconfigurations, account hacking, and a lot more.
Cloud security tools have also made it easier to stay compliant with both national and international regulations. Users can choose from multiple cloud security solutions to protect their data and applications from cyber threats. Here are some popular cloud security tools you can use to strengthen your cloud security.
List of Cloud Security Tools to Protect Cloud Environment
- McAfee
- Zscaler
- Barracuda CloudGen Firewall
- Qualys
- Rubrik
- Lookout
- Fugue
- CrowdStrike Falcon
- TOPIA
- Microsoft Entra Permissions Management
- Cisco Cloudlock
- Cloudflare Web Application Firewall
- Zerospam.eu
There are endless options available when it comes to cloud security monitoring tools. Most of these tools come with features like threat detection and prevention, identity & access management, firewall security, botnet and spyware protection, etc.
Let’s check out some of the most popular tools for protecting the cloud environment.
McAfee
McAfee helps users to keep all their data, whether on-premises or on the cloud, safe from any kind of malware and ransomware attacks. It offers features like safe web browsing, firewall security for network protection, a file shredder to delete sensitive files, etc. It also monitors the identity over the dark web for any compromised credentials.
McAfee Features
- Malware detection
- Real-time scanning of data and applications
- Firewall for home network security
- Behavioral detection to recognize and eliminate malware and zero-day digital threats
McAfee Pros and Cons
- You get encrypted storage space with McAfee
- It also offers a password manager to manage login credentials
- Spam filtering feature is not available
- Sometimes it does not create complex and unique login passwords
McAfee Pricing: No free plan available | Paid plan starts from INR ₹799.00 annually
Zscaler
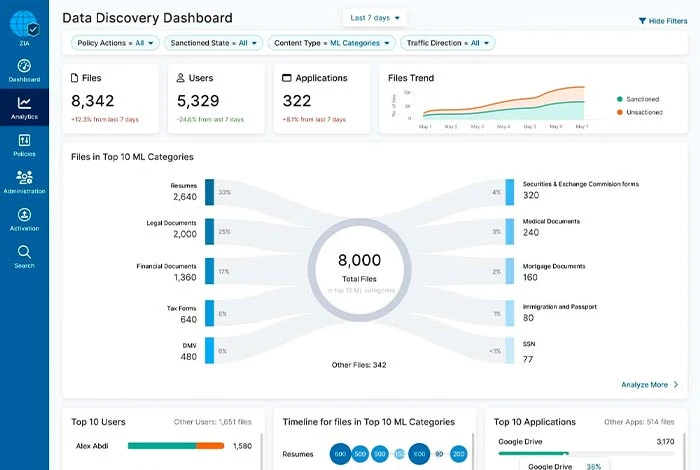
Zscaler helps organizations to secure their workload, apps, and data on the cloud while also minimizing any risk to cloud security. With it, you can segment your workload and applications, maintain compliance with cloud platforms, remediate cloud configurations, and manage permissions to access the cloud infrastructure.
Zscaler Features
- Identify excess permissions for users
- Sensitive applications segmentation
- AI-based phishing detection
- Scan the assets to minimize surface attack
Zscaler Pros and Cons
- It comes with data loss prevention (DLP) functionality for file recovery
- You can use it to keep your app-to-web and app-to-app traffic secured across both cloud and data center environments
- Transferring the workload to cloud slows the system functioning
Zscaler Pricing: Price is available on request on Zscaler’s official website.
Barracuda CloudGen Firewall
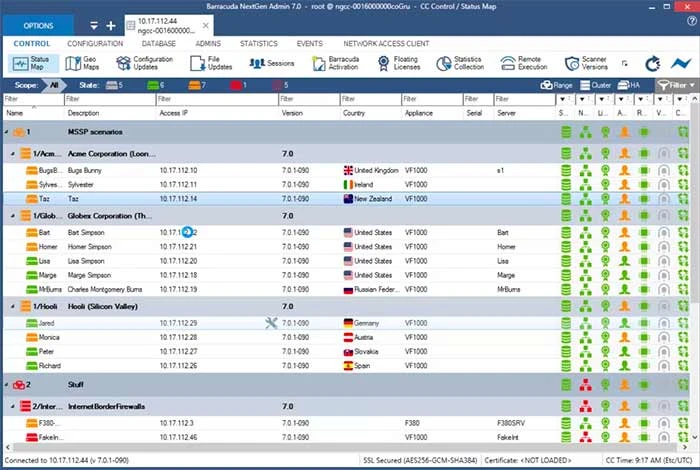
Barracuda CloudGen Firewall is a popular cloud security tool used to protect the network infrastructure against multiple network vulnerabilities like SQL injections and cross-site scripting. With features like network access control, web filtering, uplink optimization, and traffic duplication, it provides complete protection against distribution network environments.
Barracuda CloudGen Firewall Features
- Botnet and spyware protection
- Advanced threat protection
- Supports SSL interception
- Adaptive bandwidth protection
Barracuda CloudGen Firewall Pros and Cons
- Perfect to manage complex network infrastructure
- Creates secure site to site connectivity between different on-premises firewalls
- Monitoring multiple networks together might affect the system functioning
Pricing: Pricing is available on request on Barracuda CloudGen Firewall official website.

Qualys
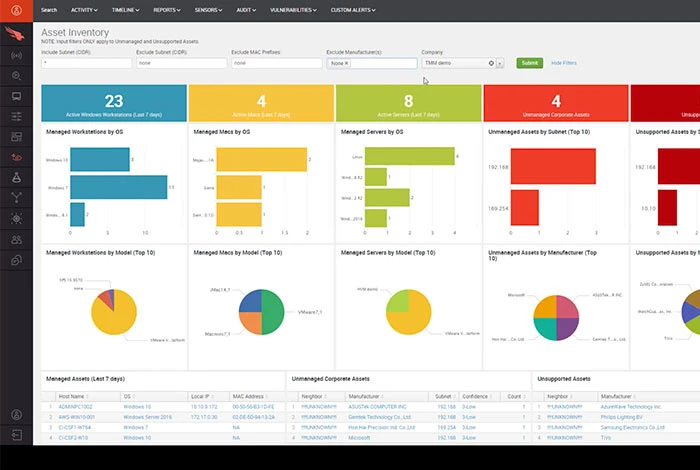
Qualys is a cloud-security solution that offers security intelligence to protect and manage Internet perimeter systems, networks, web applications, etc. It is one of the best cloud security solutions for classifying IT assets, fixing potential vulnerabilities, providing threat protection, and managing compliance with internal and external policies.
Qualys Features
- Vulnerability management
- Web application monitoring for vulnerabilities
- Multiple sensors to detect IT devices connected to network
- Endpoint issues detection and response
- File integrity monitoring
Qualys Pros and Cons
- You can easily set configuration policies for multiple environments and assets
- It deploys patches for fixing vulnerabilities in the IT system
- Scanning sometimes does not detect all the vulnerabilities
- It does not support offline deployment
Qualys Pricing: Free community edition available | Price is available on request on Qualys official website for paid plans.
Rubrik
Rubrik Cloud Security Platform helps organizations in keeping their data secure across enterprises, SaaS applications, the cloud, etc. It can be used to secure data with access-controlled backups, remediate data threats, and recover the data and application without any malware reinfection. Further, with automated threat discovery workflows, users can quickly identify threats and accelerate the recovery procedure.
Rubrik Features
- Threat and ransomware protection
- Orchestrated application recovery
- Data risk assessment
- Anomalies detection
Rubrik Pros and Cons
- It constantly monitors the data for any kind of vulnerabilities
- You can prevent any data breach for data at rest and data in-flight through encryption
- Data restoration procedure is overwhelming for Microsoft 365 applications.
- Limited options for backup snapshots.
Rubrik Pricing: Price is available on request on the official website of Rubrik
Suggested Read: List of Best Free Cloud Storage Services
Lookout
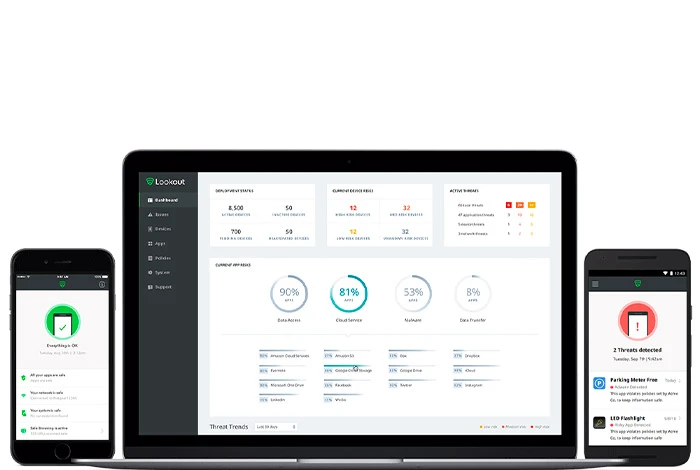
Lookout’s Cloud Security Platform ensures zero trust security to reduce data security risks, protect data, and move data securely across any environment. With its single proxy architecture, you can implement security policies and get end-to-end visibility through a centralized dashboard.
Lookout Features
- Inline data protection
- Detect and reduce cyber threats
- Telemetry intelligence for protection against unknown device
- Identify and eliminate data exfiltration.
Lookout Pros and Cons
- It helps in preventing data leakage in email, messaging apps, etc., via advanced data protection.
- Through anomaly detection, you can prevent unauthorized usage of your cloud resources
- Steep learning curve
- Data analysis is only possible through the API-integration
Lookout Pricing: No free plan available | Paid plan starts from INR 8,256.67 annually
Fugue
Fugue is a cloud security platform that helps users secure the complete cloud development lifecycle starting from its infrastructure till the runtime. It assists the security teams to stay compliant, deploy security into the cloud development, and avoid cloud misconfigurations. Its key features include support for IaC security, role-based access permissions, prioritizing remediation for every violation, etc.
Fugue Features
- Compliance automation
- Resources visualization
- Drift detection and auto remediation for vulnerabilities
- Resource data engine for capturing cloud resources configurations, relationships, etc.
Fugue Pros and Cons
- You get exportable maps of the cloud environment and its security with Fugue
- It performs security checks for GIT workflows and CI/CD pipeline
- Users have reported that it does not detect all the security vulnerabilities.
Fugue Pricing: Price is available on request on the Fugue’s official website.
CrowdStrike Falcon
CrowdStrike Falcon uses technologies like next-generation antivirus (NGAV), cyber threat intelligence, and endpoint detection and response (EDR) to protect data in multiple cloud environments. It helps eliminate cloud misconfigurations, identify and remediate threats, and protect containerized cloud-native applications. You can use it to protect endpoints, cloud workloads, identities, data, etc.
CrowdStrike Falcon Features
- Cloud security posture management
- Malware detection
- Endpoint and identity protection with threat hunting
- Manage compliance across AWS, Google Cloud, Azure, etc.
CrowdStrike Falcon Pros and Cons
- It predicts and identifies threats in the environment and delivers responses in real-time
- You can also detect malicious behavior via drift prevention or behavioral profiling
- Limited features available for identity threat detection and prevention
CrowdStrike Falcon Pricing: No free plan available | Paid plan starts from INR 24,766.72 annually
TOPIA
Topia is a global talent mobility software helping organizations to manage and deploy employees from anywhere. It also helps in managing employees’ talent mobility cycle, remote work and travel compliance, payroll, etc. Further, it offers multiple security protocols for responding to security threats, mitigating security risks through continuous assessment, and protecting confidential data through implementing security and policies.
TOPIA Features
- Access control and permissions management
- Activity monitoring
- Compliance management
- Risk assessment and management
TOPIA Pros and Cons
- You can collaborate with other team members in real-time to frame policies
- It also offers disaster recovery plans to recover the organizational data
- Limited features for data security
- Users have experienced technical issues while doing risk assessment
TOPIA Pricing: Price is available on request on Topia’s official website.
Suggested Read: What is Data Security in Cloud Computing: Best Practices & Challenges
Microsoft Entra Permissions Management
Microsoft Entra Permissions Management is a CIEM tool to manage permissions to access an organization’s cloud network. It provides visibility and control over all identities and resource permissions in Microsoft Azure, Google Cloud Platform (GCP), and Amazon Web Services (AWS). With it, you can constantly monitor the permissions to prevent unauthorized access to the cloud.
Microsoft Entra Permissions Management Features
- Permissions risk evaluation and management
- Real-time visibility into cloud permissions
- Anomaly and outlier detection to prevent data breaches
- Create and implement security policies across all cloud environments
Microsoft Entra Permissions Management Pros and Cons
- It automatically detects any anomalies through machine learning
- You can manage permissions for multiple cloud environments from a single solution
- Takes time to deploy multiple files over the cloud
- It does not offer support for IDS (Intrusion Detection System) to constantly monitor network traffic
Pricing: No free plan available | Paid plan starts from INR 820.00/ resource/month
Cisco Cloudlock
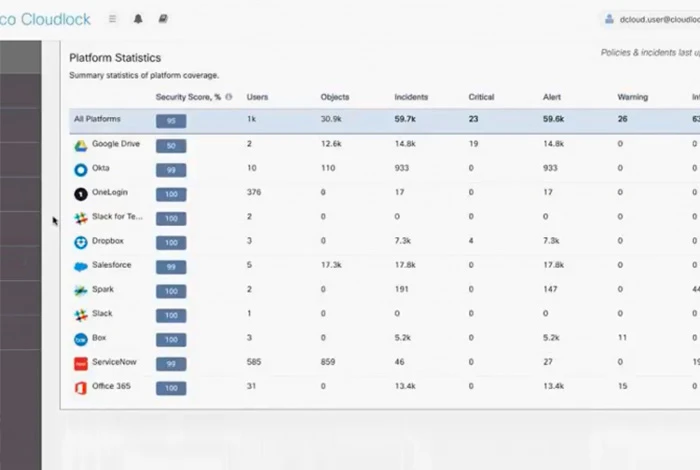
Cisco Cloudlock is a cloud access security broker (CASB) to securely move your data and applications on the cloud. It is one of the best cloud security solutions that helps organizations meet compliance regulations while eliminating any data breaches.
Cisco Cloudlock Features
- Identify and secure sensitive data
- Real-time monitoring of cloud apps and data
- Complete visibility into cloud activities
Cisco Cloudlock Pros and Cons
- Detects all types of threats over the network through cloud-delivered analytics.
- Support for zero trust micro segmentation to prevent threats spreading across applications
- Alert mechanism works a bit slow
Pricing: Price is available on request on Cisco Systems Cloudlock official website
Cloudflare Web Application Firewall
Cloudflare’s Web Application Firewall (WAF) helps users in protecting their websites and applications from threats like SQL injection, zero-day attacks, cross-site scripting (XSS), etc. It can also be used to manage different bots in real-time by using the internet properties data available on Cloudflare.
Cloudflare Web Application Firewall Features
- OWASP rules to stop common application threats
- Automatically blocks unexposed credentials for your website
- Role-based access permissions
- Bot management
Cloudflare Web Application Firewall Pros and Cons
- It supports prioritizing your networks
- Secures websites and applications and ensures that legitimate traffic is not affected with DDoS Protection
- Limited support for image optimization
- Every website domain supports only a single script.
Cloudflare Pricing: No free plan available | Paid plan starts from INR 1,651.80/month
Zerospam.eu
zerospam.eu is an e-mail security tool that lets you filter the domain’s mailboxes to block and remove messages containing spam, phishing, viruses and malware. It can also be used to archive messages and retrieve them when required.
Zerospam.eu Features
- Malware and phishing mail detection
- Protection against virus
- Spam messages removal
- Screening messages for spam
Zerospam.eu Pros and Cons
- It performs risk assessment of all the messages for any type of threats
- Protects your email against all types of viruses
- Sometimes spam messages are shown in the main mailbox due to technical glitch.
Pricing: No free plan available | Paid plan starts from INR 439.20/ month
Suggested Read: What is Cloud Migration? Benefits, Types & Strategy
Why Do DevOps Need Cloud Security Solutions?
Previously, organizations used to deploy security protocols only at the end of product development, which hampered the product deliverability time. However, with the coming of various cloud security solutions, DevOps can work on the security part of the applications while preparing them to move to the cloud infrastructure. Thus, making it easier to deploy applications on the cloud quickly.
Types of Cloud Security Tools
There are six different types of cloud security solutions you can consider securing your cloud workload, apps, and data.
- CASB – Cloud Access Security Brokers: CASB can be an on-premises or cloud-based software that includes security policy enforcement endpoints put between the consumer’s cloud infrastructure and the cloud service provider. This helps enforce security policies via risk identification and regulatory compliance when the cloud data is accessed.
- SAST – Static Application Security Testing: SAST solutions are used to analyze any application source code to find signs of security vulnerabilities and suspicious activities.
- SASE – Secure Access Service Edge: It is a kind of network architecture that comes with VPN, SD-WAN, and security features like firewalls to strengthen network security.
- CSPM – Cloud Security Posture Management: CSPM tools help in identifying and remediating security and compliance risks by automatically providing visibility into the cloud infrastructure. It also helps in detecting threats and remediating misconfigurations for different public cloud environments.
- CWPP – Cloud Workflow Protection Platforms: It helps keep the workloads protected in both modern cloud and data center environments. It can be used to ensure the security of physical machines, VMs, containers, serverless workloads, etc.
- CIEM – Cloud Infrastructure Entitlement Management: Cloud Infrastructure Entitlements Management solution helps in managing permissions and privileges for the user identities in one or multiple cloud environments. It enables you to detect and eliminate any type of risk resulting from unauthorized access or permissions.
Conclusion
Cloud security tools will not only help organizations in detecting vulnerabilities but also eliminate them to strengthen the security of the digital assets. Further, through risk assessment, organizations can constantly monitor their applications and data to prevent security breaches in the future.
Related Categories: Cloud Security Services | Cloud Management Service | Data Management Software | Encryption Software
FAQs
What are the top 5 security in cloud computing?
There are multiple types of security in cloud computing to prevent any data breach and secure the cloud environment. Some of these include data masking, secure deletion, data encryption, access control, identity and authentication, etc.
What are cloud security tools?
Cloud security tools help in protecting the cloud infrastructure including the workloads, applications, data, and networks against any type of cyber threat. With these tools, you can prevent data theft, monitor networks for any vulnerabilities, restrict internet access, and much more.
Are cloud services secure?
Yes, most cloud services are secure and use advanced security protocols such as SSL or TLS to keep your data protected and safe from any data breach. However, a data breach might occur if you do not use advanced security and the hacker bypasses the security protocols,
What are the best cloud security tools?
You can choose from different types of cloud security tools to keep your cloud infrastructure safe and protected from any data breaches. Some of the top choices are Barracuda CloudGen Firewall, Zerospam, Rubrik, Zscaler, Cyscale, etc.
5.What are the top cloud security tools?
Top cloud security tools use multiple security protocols to keep your data and IT assets protected. Some of the top tools you can consider are Cloudflare, Zerospam, TOPIA, Trend Micro Cloud One, Rubrik, Orca Security, etc.
What are the four areas of cloud security?
The four areas of cloud security include cloud data visibility, cloud data management, access management for cloud data & applications, and compliance management.
Which cloud service is most secure?
The choice for the safest cloud service would depend on the type of security features it offers to its customers such as data encryption, firewall, or different authentication methods. However, some of the most secure cloud services include IDrive, pCloud, Sync.com, Microsoft OneDrive, Google Drive, Egnyte Connect, etc.
Who is responsible for security in the cloud?
Ensuring cloud security is the responsibility of the service provider. The provider must implement multiple security protocols such as data encryption, permission management, or risk assessment to protect the cloud’s data, applications, and networks from any data breaches.
Varsha is an experienced content writer at Techjockey. She has been writing since 2021 and has covered several industries in her writing like fashion, technology, automobile, interior design, etc. Over the span of 1 year, she has written 100+ blogs focusing on security, finance, accounts, inventory, human resources,... Read more